What is Zero Trust Approach (ZTNA)?
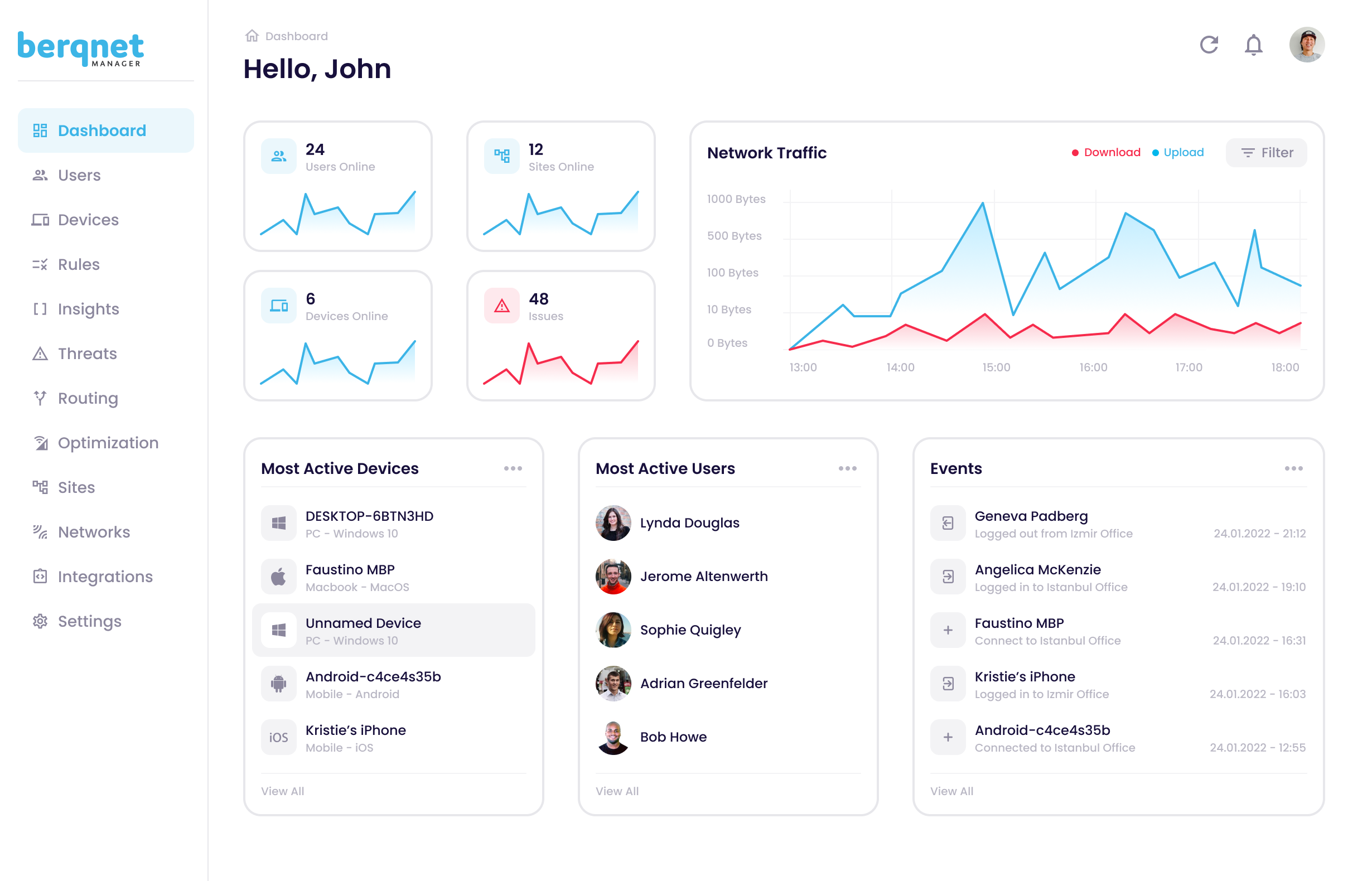
In the Berqnet SASE Zero Trust approach, an extra layer of security is used to authenticate users trying to connect to the network to ensure that only trusted users and devices are connected to the network. In addition to static controls such as user name, password and one-time password, behavior-based data such as connection time, operating system / screen size / location of the connected device are also used in the authentication process.
In each connection attempt, the user's current behavior-based data is compared with the data in a certain period and the risk score is calculated using artificial intelligence. When the risk score exceeds a certain level, the user is not allowed to access network resources.
Thanks to the micro-segmentation capability of the Berqnet SASE platform's firewall, access permissions of users and devices to critical resources can be determined in detail. In this way, sensitive resources that need to be protected are secured at a high level.
The Benefits of Zero Trust Approach (ZTNA) Technology to Your Business
Unique Advantages of Remote Connecting Technology in Berqnet SASE Compared to Traditional VPN Technology
More Secure Remote Access
More secure remote access is provided by verifying the user with behavioral analysis and isolating unidentified devices.
Risk Reduction
By closing security gaps with tighter access controls, it controls lateral movement in the network and reduces possible risks.

Data Security
It provides stronger access controls and protection for applications and data, whether in the cloud or in the on-premises data center.
Get to know Berqnet SASE, the cyber security product developed with the latest technologies.
Resources That Might Interest You
What is ZTNA? - Whitepaper
Especially in the recent period following the pandemic, Zero Trust Network Access (ZTNA) has become one of the concepts that are frequently mentioned in the network and cyber security world. You can review this whitepaper to get to know ZTNA technology closely.
Download for Free
What is SASE? - Whitepaper
It is getting harder and harder to provide your cyber security with traditional methods. New technologies developed in accordance with cloud-based and centralized management capabilities are already meeting the most important needs of the future. You can review this whitepaper to get to know SASE technology closely.
Download for Free
Key Differences Between SD-WAN and SASE - Whitepaper
The latest trends in cybersecurity may be replaced by a new technology tomorrow. So, can you decide what technology you need right now? This whitepaper explains to you the differences between SD-WAN and SASE in detail. You can review this whitepaper to better understand the differences between the two technologies.
Download for Free